Latest
Reverse chronological feed of all published articles.

FeaturedOriginal
Josef Prusa warns Chinese 3D printing software poses massive security risks — Bambu Lab allegedly violates AGPL license with an un-auditable network 'black box'
AI Summary
Josef Prusa warns of significant security risks from Chinese 3D printing software, citing Bambu Lab's AGPL violations.
Why Featured
This news highlights critical security concerns in 3D printing software, signaling developers and PMs to prioritize compliance and transparency in their projects to mitigate risks.

A 45,000-person labor strike at Samsung’s memory chip plants could throw a wrench into the AI boom
AI Summary
A massive labor strike at Samsung's memory chip plants may disrupt the AI industry's growth.
Why Featured
The Samsung labor strike threatens supply chains for critical memory chips, potentially delaying AI projects and increasing costs for developers, PMs, and investors reliant on these components.

FeaturedOriginal
Grafana GitHub Token Breach Led to Codebase Download and Extortion Attempt
AI Summary
Grafana reported a GitHub token breach allowing codebase access but no customer data was compromised.
Why Featured
The Grafana GitHub token breach highlights the critical need for robust security practices in software development to protect intellectual property and prevent extortion attempts.

'They will just milk you until you're dry': New Yorker loses $20,000 to a fake job offer that started with a simple text
AI Summary
A New Yorker lost $20,000 to a scam job offer initiated by a text message.
Why Featured
This incident highlights the increasing sophistication of scams, signaling developers and PMs to prioritize security in job-related platforms and investors to be wary of potential losses in the tech job market.

FeaturedOriginal
Funnel Builder Flaw Under Active Exploitation Enables WooCommerce Checkout Skimming
AI Summary
A critical vulnerability in Funnel Builder for WordPress is exploited to steal WooCommerce payment data.
Why Featured
This vulnerability highlights the urgent need for developers and PMs to prioritize security measures in e-commerce platforms to protect sensitive payment data from exploitation.

BMO Capital Maintains an Outperform Rating on Check Point Software Technologies Ltd. (CHKP)
AI Summary
BMO Capital maintains an outperform rating on Check Point Software Technologies Ltd. (CHKP).
Why Featured
BMO's outperform rating on Check Point signals confidence in its cybersecurity solutions, indicating potential growth opportunities for developers, PMs, and investors in the AI-driven security market.
I’ve been studying Big Tech for a long time. What just happened with Anthropic and the Pentagon terrifies me
AI Summary
The Anthropic-Pentagon situation highlights the urgent need for regulatory action in Big Tech.
Why Featured
The Anthropic-Pentagon situation signals an impending regulatory shift in AI, which developers, PMs, and investors must navigate to ensure compliance and strategic positioning in a rapidly evolving landscape.

FeaturedOriginal
AI data centers trigger massive 'irreversible' 76% electricity price spike in largest US region — federal watchdog demands tech giants pay for their own power infrastructure
AI Summary
AI data centers cause a 76% electricity price spike in the US, prompting federal scrutiny.
Why Featured
The 76% electricity price spike due to AI data centers signals potential increased operational costs for developers and PMs, while investors must consider infrastructure liabilities affecting tech giants' profitability.
FeaturedOriginal
AI data centers require 36 times more fiber than designs with standard servers — severe glass shortages push cable lead times out to a full year
AI Summary
AI data centers need 36 times more fiber than standard servers, causing severe supply shortages.
Why Featured
The demand for fiber in AI data centers highlights critical supply chain challenges, impacting infrastructure costs and project timelines for developers, PMs, and investors in the AI sector.

FeaturedOriginal
First Apple M5 memory exploit discovered using Anthropic AI, gives root access on MacOS — Claude Mythos helps security researchers bypass Memory Integrity Enforcement
AI Summary
The first exploit for Apple M5 architecture allows root access on MacOS using Anthropic AI.
Why Featured
The discovery of an Apple M5 memory exploit using Anthropic AI signals potential vulnerabilities in MacOS, highlighting the need for developers and PMs to prioritize security in their applications.

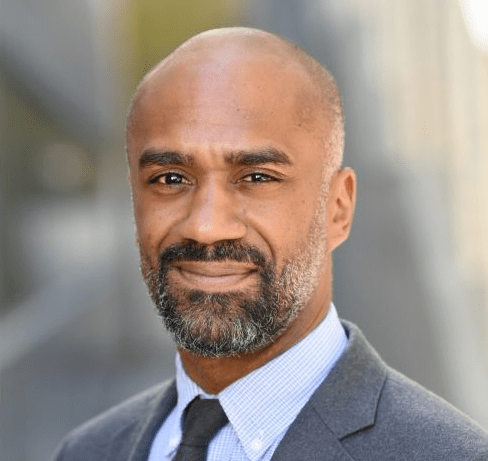
Would you hire the lawyer who just got sanctioned for using AI?
AI Summary
Lawyers face sanctions for misusing AI, leading to fabricated evidence and client harm.
Why Featured
This news highlights the legal risks of AI misuse, signaling to developers and PMs the need for ethical guidelines and to investors the importance of compliance in AI-driven solutions.
FeaturedOriginal
A hotel check-in system left a million passports and driver’s licenses open for anyone to see
AI Summary
A hotel check-in system exposed a million passports and licenses due to public cloud storage.
Why Featured
This incident highlights the critical need for robust data security practices in cloud storage to protect sensitive user information, impacting developers, PMs, and investors focused on privacy and compliance.

FeaturedOriginal
Tesla reveals two Robotaxi crashes involving teleoperators
AI Summary
Tesla's crash reports highlight challenges faced by its robotaxi program involving teleoperators.
Why Featured
Tesla's robotaxi crashes signal potential regulatory hurdles and safety concerns, impacting developers and PMs focused on autonomous vehicle technology and investors assessing the viability of robotaxi investments.

FeaturedOriginal
Analyst Report: Northrop Grumman Corp
AI Summary
Analyst report highlights Northrop Grumman's strong performance and growth potential in defense sector.
Why Featured
Northrop Grumman's strong performance signals robust investment opportunities in defense tech, crucial for developers, PMs, and investors focused on emerging defense AI applications.

FeaturedOriginal
Turla Turns Kazuar Backdoor Into Modular P2P Botnet for Persistent Access
AI Summary
Turla has developed a modular P2P botnet from its Kazuar backdoor for stealthy, persistent access.
Why Featured
The emergence of Turla's modular P2P botnet signals a new level of sophistication in cyber threats, highlighting the need for developers and PMs to prioritize security in their applications.

FeaturedOriginal
Phantom Data Centers Didn't Break the Power Grid—They Proved it Was Already Broken
AI Summary
Phantom data centers highlighted existing vulnerabilities in the power grid rather than causing outages.
Why Featured
The revelation of vulnerabilities in the power grid emphasizes the need for developers and PMs to prioritize resilient infrastructure, while investors should consider the implications for energy sector investments.

FeaturedOriginal
US orders travelers on Air Force One to throw away gifts, pins, and burner phones after China trip
AI Summary
Travelers on Air Force One discarded gifts and devices after a China summit for security reasons.
Why Featured
This highlights the increasing importance of cybersecurity measures, signaling developers and PMs to prioritize secure communication solutions and investors to consider opportunities in security tech.

FeaturedOriginal
Google floats reduced initial 5GB free cloud storage limit, users claim — 15GB to require extra security measures, company confirms it is 'testing a new storage policy for new accounts'
AI Summary
Google is testing a reduced 5GB free cloud storage limit to enhance security for new accounts.
Why Featured
Google's potential reduction of free cloud storage to 5GB signals a shift towards stricter security measures, impacting developers, PMs, and investors by necessitating adjustments in storage strategies and cost management.

Pope Leo warns of ‘spiral of annihilation’ as AI warfare leads to symphony of destruction
AI Summary
Pope Leo warns that AI warfare could lead to catastrophic destruction and calls for peace.
Why Featured
Pope Leo's warning highlights the urgent need for developers and PMs to prioritize ethical AI in warfare, signaling potential regulatory shifts that investors should monitor closely.

Americans would rather live near a nuclear power plant than a data center—by a lot
AI Summary
Americans prefer living near nuclear power plants over data centers due to fears of AI and pollution.
Why Featured
This preference signals potential regulatory challenges for data centers, impacting developers and PMs in site selection, while investors may need to reassess the viability of data center projects.

FeaturedOriginal
Four OpenClaw Flaws Enable Data Theft, Privilege Escalation, and Persistence
AI Summary
Four OpenClaw vulnerabilities enable data theft, privilege escalation, and persistent backdoor access.
Why Featured
These OpenClaw vulnerabilities signal critical security risks that developers must address, PMs need to prioritize in project planning, and investors should consider when assessing software reliability.

FeaturedOriginal
What 45 Days of Watching Your Own Tools Will Tell You About Your Real Attack Surface
AI Summary
Trusted administrative tools pose significant security risks as they are exploited by modern threat actors.
Why Featured
Understanding the vulnerabilities in trusted tools is crucial for developers and PMs to enhance security measures, while investors should note the potential risks impacting product reliability and market trust.

'Everybody and their mother is using these things': AI note-takers are creating a legal time bomb in boardrooms
AI Summary
AI note-takers in boardrooms raise potential legal risks and privacy concerns.
Why Featured
The rise of AI note-takers in boardrooms signals urgent legal and privacy challenges that developers, PMs, and investors must navigate to mitigate risks and ensure compliance.

FeaturedOriginal
TanStack Supply Chain Attack Hits Two OpenAI Employee Devices, Forces macOS Updates
AI Summary
OpenAI reports a supply chain attack affecting two employee devices, but no data was compromised.
Why Featured
The supply chain attack on OpenAI highlights the importance of robust security measures for developers and PMs to protect sensitive data and maintain trust in AI systems.

FeaturedOriginal
On-Prem Microsoft Exchange Server CVE-2026-42897 Exploited via Crafted Email
AI Summary
Microsoft Exchange Server CVE-2026-42897 is actively exploited, linked to a spoofing vulnerability.
Why Featured
The exploitation of CVE-2026-42897 in Microsoft Exchange highlights the urgent need for developers and PMs to prioritize security updates, impacting investment decisions in enterprise software solutions.
·